Do you want to learn about cybersecurity or internet security? In our complex world of digital tools, attackers and defenders, basic rules can help you get through. Basic cybersecurity training goes a little a long way in helping you understand the essentials of protecting digital assets.
To get through, you need to ensure you are equipped with the latest information and tools available in the cybersecurity world. This is where the following top 5 cybersecurity courses will be helpful. We have put together a brief evaluation of how they can help you become a cybersecurity and data privacy expert.

Why Cybersecurity Skills Are Essential
“So, what is cybersecurity? It is no longer just for tech nerds who enjoy hacking in dark rooms. With everything going advanced, from work to shopping to mingling, safeguarding information is essential for everybody.
You’ve probably heard about all the data breaches that have occurred at banks, hospitals, and even governments. That’s where cybersecurity experts come in. Organisations need individuals who act like programmers to safeguard their frameworks and information.
In addition, the demand for cybersecurity expertise is only growing as cloud computing and remote work become more common.
Wondering how to become a cybersecurity expert? A few strong courses can assist you in getting certified and stepping up your abilities
Will the cybersecurity courses help in expanding your skill set?
There are several benefits and disadvantages that may confuse you and hinder your ability to make a decision. So, here is a brief comparison that will help you decide. It covers some of the key benefits and disadvantages of pursuing a cybersecurity course.
Advantages and disadvantages of pursuing a cybersecurity course:
| Advantages | Disadvantages |
| Increased awareness of and authority on the subject. | Time-consuming. |
| Increased understanding of prevention measures for certain cyberattacks, legal fines, litigation and negligence | Can require a subscription to the platform offering the training |
| Creates clarity on the legal requirements expected of organisations on the subject | Different legal courses may be needed depending on the extent of specialisation and depth you want to aim for |
| You may be able to offer privacy advice to organisations in a professional capacity |
We can clearly conclude that yes, completing cybersecurity courses will help you by enhancing your expertise and knowledge on the subject. This knowledge can be extremely beneficial to the organisation that a course seeker is part of. The training may help in preventing litigation and legal issues by enabling the user to implement the appropriate prevention measures in their organisation.
Organisations can reduce their overall expenses and cybersecurity issues with the help of these newly trained individuals. So, if you want to be a greater asset for your organisation or develop your current skill set to improve your resume then these courses can help make you a very sought-after resource.
Choosing the Right Cybersecurity Course: What to Look For
Now, let’s discuss what is important before enrolling in any random course. You should ensure you spend your time and money appropriately because not all courses are equal. What you should be looking out for is as follows:
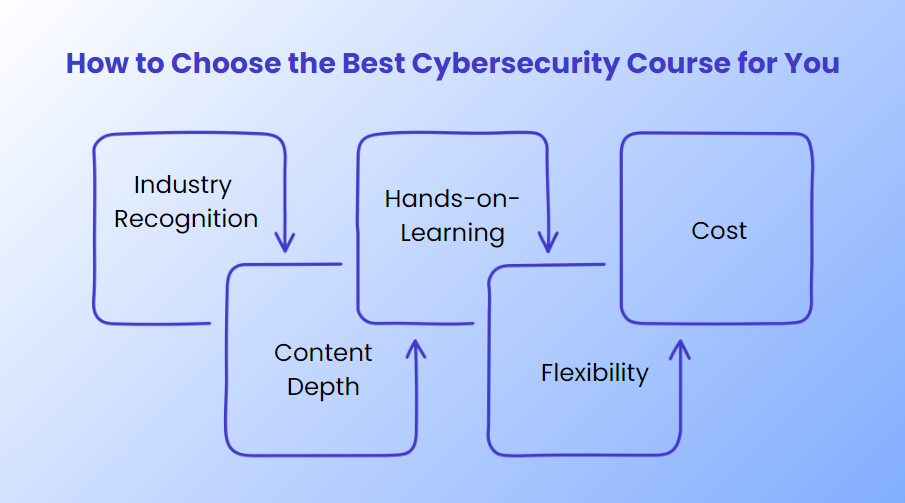
Industry Recognition: How much of an impact does the course have on cybersecurity professionals?
Content Depth: Is it designed for novices or experts with a high experience level?
Hands-on Learning: Practical labs or real-world tasks to reinforce theoretical principles are examples of hands-on learning.
Flexibility: Is the course strictly planned, or does it allow self-paced learning?
Cost: Is it worthwhile to spend on this course? Do you have any opportunities for financial aid?
While considering these requirements, let’s examine some of the best cybersecurity certification courses that will significantly improve your employment prospects.
Here are five of the best cybersecurity certifications to boost your career:
1. Certified Information Systems Security Professional (CISSP)
The CISSP certification is like the Rolls-Royce of cybersecurity certs. If you’ve been in the field for a while and want to enhance your skill set, this is the one.
This course is not for beginners; it is designed for experienced professionals. If you’re just beginning, wait before taking this step.
CISSP focuses on:
- Security and Risk Management
- Asset Security
- Security Architecture and Engineering
- Communication and Network Security
- Identity and Access Management
- Security Assessment and Testing
- Security Operations
- Software Development Security
CISSP is globally recognised and highly valued, often leading to high-paying roles in cybersecurity management.
2. Certified Ethical Hacker (CEH)
Ethical hacking courses like the CEH certification teach how hackers think. This course offers hands-on cybersecurity training. You learn how to think like a hacker so you can protect your organisation’s systems from actual cybercriminals. This course is perfect if you prefer a learning style that involves active problem-solving and real-world scenarios.
What You’ll Learn in CEH:
- Reconnaissance Techniques
- Gaining and Maintaining Access
- System Hacking
- Malware Threats
- Social Engineering
- Denial-of-Service Attacks
- Hacking Wireless Networks
- Evading IDS, Firewalls, and Honeypots
3. CompTIA Security+
CompTIA Security+ is the best starting point for beginners. Its foundation course in cybersecurity provides a broad overview of cybersecurity fundamentals, from threat detection to cryptography, without requiring previous knowledge.
What You’ll Learn in CompTIA Security:
- Threats, Attacks, and Vulnerabilities
- Technologies and Tools
- Architecture and Design
- Access Management
- Risk Management
- Cryptography
4. Certified Cloud Security Professional (CCSP)
Everything is moving to the cloud these days. The CCSP certification helps answer this question if you’ve ever wondered who safeguards cloud-based data. This course focuses on cloud security, a skill in demand right now. Expertise in this field is like finding gold as more businesses move their infrastructure to the cloud.
What You’ll Learn in Certified Cloud Security Professional (CCSP):
- Cloud Concepts, Architecture, and Design
- Cloud Data Security
- Cloud Platform and Infrastructure Security
- Cloud Application Security
- Cloud Security Operations
- Legal, Risk, and Compliance
5. Google Cybersecurity Professional Certificate
Google’s Cybersecurity Professional Certificate is a great option if you’re new to tech or serious about hands-on experience. You’ll dive deep into essential topics like network security, cryptography, and incident response training to handle security incidents effectively.
This certification is especially valuable for people looking to work in government or corporate security, making it a significant step if that’s your career goal.
What You’ll Learn:
- Foundations of Cybersecurity
- Network Security and Database Vulnerabilities
- Incident Response
- Penetration Testing
- Security Policy and Risk Management
This affordable, flexible, and Google-backed course focuses on equipping you with cybersecurity skills for immediate job readiness.
Why Online Cybersecurity Courses Are a Game-Changer
One of the best things about these courses is that many are designed to support cybersecurity remote jobs. You don’t need to quit your day job. Online cybersecurity classes give you the flexibility to learn when and how it suits you. You can still handle your 9-to-5, your side hustle, or whatever else you’ve got while earning a certificate that can open doors to a new career.
Cybersecurity Career Paths (and What You Can Earn)
Now that you’ve finished the class and passed the tests, what comes next? The extraordinary news is that network safety offers a wide variety of vocation choices. Some common roles you might consider are
- Cybersecurity Analyst
- Penetration Tester
- Security Architect
- Cloud Security Specialist
Now, let’s talk about the cybersecurity salary range
Depending on where you are, entry-level cybersecurity jobs typically start at between $70,000 and $90,000.
Higher-level positions, including high-paying cybersecurity jobs, can easily pay six figures as you advance in your career and obtain high-level certifications..

Wrapping It Up
No matter which course you choose, getting started is important. Cybersecurity is a rapidly growing field, and the right training can lead you to success.
Whether you’re just starting out or looking to take your career to the next level, there’s a course for you. Do your research, pick the course that aligns with your goals, and don’t be afraid to invest in yourself. The world of cybersecurity is growing fast, and trust me, you want to be a part of it.
So, having the basic and advanced knowledge of cybersecurity (Internet security) and the digital world is of essential importance to all businesses in the current environment. Empower your skillset to deal with the contemporary digital challenges via these courses now.
